So here is the first post of a (hopefully long) series about pentester tricks, from my very own field experience. Enjoy!
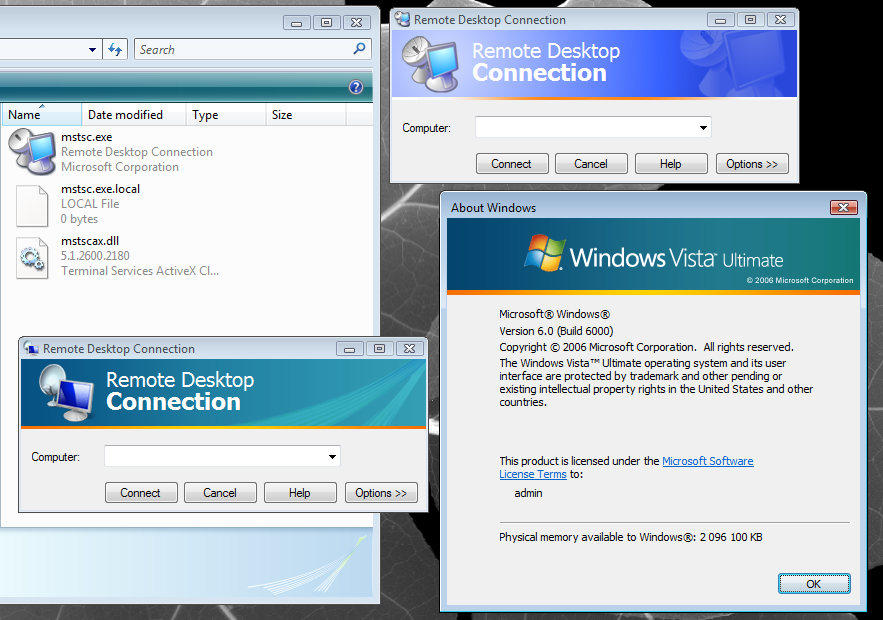
Trick #1 : using RDP Client 5 on Vista
RDP Client 5 has a great advantage over RDP Client 6 : it allows connecting to the remote target without giving any credential ; thus the pentester can get access to server version, computer name and trusted domains, without leaving any track in the security audit trail.
However RDP Client 6 has been pushed on Windows Update quite a while ago, and is required in some cases (like Windows Vista/2008 Remote Desktop with full security options ... which are recommended given flaws found in previous versions of RDP protocol).
Fortunately, it is quite easy to make both clients living together. RDP Client 5 consists of only 2 binaries : MSTSC.EXE and MSTSCAX.DLL. The trick is to copy both files, and to create a MSTSC.EXE.LOCAL file in the same directory. This will force MSTSC.EXE to load libraries from the current directory instead of the global system directory.
References: [1] [2]

No comments:
Post a Comment